Evacuations from High-Risk Locations Call +44 (0)1202 308810 or Contact Us →
Penetration Testing: Demonstrate your Customer’s Data is Safe

Win Your Customers’ Trust
Data is a valuable commodity and the consequences of a data breach can cause not only a significant fine from the ICO, but irreversible reputation damage for a company too. Penetration Testing is important for organisations of all sizes. A well-structured and scoped penetration test can help reduce the cyber risk exposure of an organisation as well as protect both the organisations and their client’s data. It supports Data Protection compliance by evidencing regular testing (a GDPR requirement). Penetration Testing also assists with marketing. Once all the fixes are in place, the retest report can be a valuable marketing asset.
How Penetration Testing Works
A penetration test from Solace Cyber, sometimes known as a pen test, is the process of replicating a cyber attack performed by a cyber security specialist. Pen testing will uncover security weaknesses by using the same methods that a hacker would, by replicating their approach as closely as possible against new vulnerabilities and exploits that become available daily.
A critical part of our testing methodology is to show you you not only what we found, but how we found it. Knowing how we found the issues is the key to your continual improvement, which is why we follow our tried and tested 6-step high level methodology for every penetration test.
Experts in Finding Vulnerabilities Your IT Team May have Missed
Our team of experts spend 3 months a year keeping their skills up to date, meaning we are always one step ahead of the evolving cyber security threats and have a deep understanding of the latest threat ecosystem. This means we can evaluate your business and identify your vulnerabilities, configuration weakness and gaps in protection to the highest quality.
We use a highly respected Council of Registered Ethical Security Testers (CREST) affiliated penetration testing service, followed up with a complimentary strategic session with our cyber security specialists once you have your results to help address any issues identified.
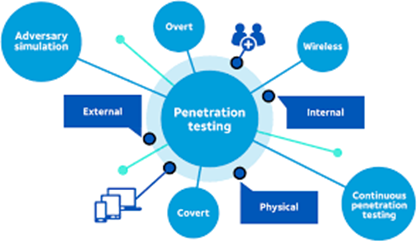
Our services cover all types of Penetration Test including, but not limited to:
- API and Backend Systems
- Infrastructure – Internal, External & Cloud
- Mobile Applications – Android, iOS & Windows
- PCI-DSS
- Physical
- Remote Access & VPN Systems
- Social Engineering
- Web Applications – from Blogs to Ecommerce
The Key to a Successful Penetration Test
In-depth planning is a critical step to ensure a successful penetration test. This is one of the most critical steps in ensuring success in your penetration test. This is where we work together to define the scope, and the goal of the test rigorously to give you assurance every angle has been covered.
During the scoping call for your penetration test, we are looking to identify exactly what needs testing, how complex it is and how much time we will need to use to complete the penetration test to the best of our capability. We will also look to identify the goal of the penetration test. The goal could be as simple as “identify all the exploitable vulnerabilities”. It could be a lot more complex such as “pivot through an exploited host and attack the internal network to gain access to client data.”
Having a well-defined scope is the key to the success of your penetration test. Therefore, we can never answer the question of “how much is a penetration test” until we have had a call to discuss your penetration testing scope.
Speak to a cyber security specialist
Enquire using the form below